
Engineering Localization
CAD/CAM/DTP
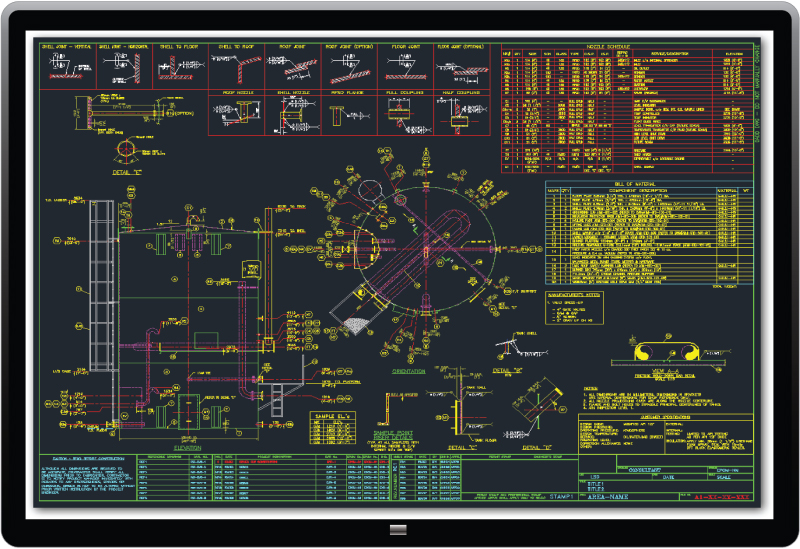
Engineering documentation plays a fundamental role in diverse production cycles. Localizations in this industry leaves no room for errors
Our professionals have a comprehensive expertise working in many engineering fields, such as:
IT, industrial machinery, power generation, petrochemical, life science, or civil engineering, but not limited to. Having skills, knowledge and education within the primary sections of engineering, opening the world of knowledge, capable enough to deal with many sub-branches of engineering industry
Engineering phrases and terminology can’t be translated adequately by someone unaccustomed with your industry. Terms and phrases are often more complex than in many other documentation, what makes inescapable that it will be translated and published accurately.
Never mind the volume or size of engineering localization tasks. We are a technology born company, so we can deal successfully with any obstacles related to the type or size of orders.
INFORMATION AND DATA SECURITY
We prioritize the security of your data and our resources with exceptional diligence. Recognizing the need to protect certain documents and information from unprivileged individuals and automated systems, we have implemented rigorous safety controls and methodologies across our business units:
- We don’t use cloud based storage services (Google, Dropbox etc.) for sensitive data ( unless specified otherwise by Customer)
- We don’t use outsourced SMT (Statistical Machine Translation Engines) unless specified otherwise by Customer
- We don’t Build, Train, and Deploy Machine Learning systems and process datasets with use of cloud based third parties engines unless specified otherwise by Customer
- We are using only secured transmission protocols for external communication
- Strong files encryption within local storages and Distributed DMS
- Robust access privileges to our online platforms (profiles, roles, sharing rules)
- Access control on databases records level
- MFA authentication for all access to sensitive data
- Data destruction and disposal procedure in place
- Intrusion prevention system
- Multilayer data loss prevention (DLP) systems and procedures in place
- Data anonymization procedures (important while outsourcing projects)
- Regular Security & Confidentiality Audits
- Data Centers in Europe and Asia (depending on data security requirements, certain DC is selected)
- Full GDPR compliance
- Data protection compliance in line with regulations of the countries out of Euro-zone